Elliptic curves are used in cryptography mainly because of DLP i.e. it’s infeasible to calculate from .
Pairing helps to compute certain complicated equations on EC points. Traditional EC math lets anyone check linear constraints on the number (eg. checking ), but pairing lets you check quadratic constraints ( is checking ).
This makes DDH (Decision Diffie-Hellman) problem very easy to compute using pairings. Also DLog reduction becomes computably feasible if not done on extension fields of Finite Field as we want the target group to be sufficiently bigger so that it’s not possible to do DLog reduction.
is a function defined on EC points. This is the pairing. Also known as bilinear map. It is called as bilinear because it satisfies following constraints, i.e. it doesn’t matter if we apply group law first and then map, or map then group law:
- : This property is called Non-Degeneracy. If whenever is neutral element, then either is neutral.
The pairing is linear in both constraints. So, EC Pairing is a function that takes a pair of points on an elliptic curve and returns an element of some other group, called the target group.
Example: , where →
Note: and can be any arbitrary operators. It doesn’t matter what symbols are used in abstract mathematics as long as they obey the properties of associativity, commutativity and reflexivity.
However, such simple pairings are not suitable for cryptography as its trivial to divide, compute logarithms and other computations. Simple integers can’t be used in a field having terms like public-private keys or one-way functions because anyone can go back to knowing and . Thus, we require numbers that can essentially function as “black boxes” or it’s only possible to do simple arithmetic like addition, subtraction, multiplication and division on them and nothing else. That’s where ECs and EC-points come in.
Frobenius endomorphism
Frobenius endomorphism maps EC point to another point:
full r-torsion groups has two interesting subgroups: namely,
- can also be seen as -tosion group given by mapping un-extended elliptic curve point to itself.
Pairing groups
and are subgroups given from Frobenius endomorphism on torsion subgroups of ECs.
The reason why Bilinear map works?
First, we look into the concept of divisors.
Weil Pairing
Tate Pairing
Miller’s Algorithm
MOV Attack
MOV attack refers to the transfer of DLP over EC to finite field where it’s much easier to solve. This is related to the embedded degree of the EC.
Embedded Degree of an EC refers to the minimum value of k for which , where p = prime used for the field and n = order of the curve. This is actually called an attack because DLP shouldn’t be solvable on ECs and thus for curves used throughout the cryptographic primitives, value of k is unreasonably large such that pairings are computably infeasible to compute.
Complexities Assumptions on Bilinear Groups
- Discrete Log problem is still difficult if target group is sufficiently large.
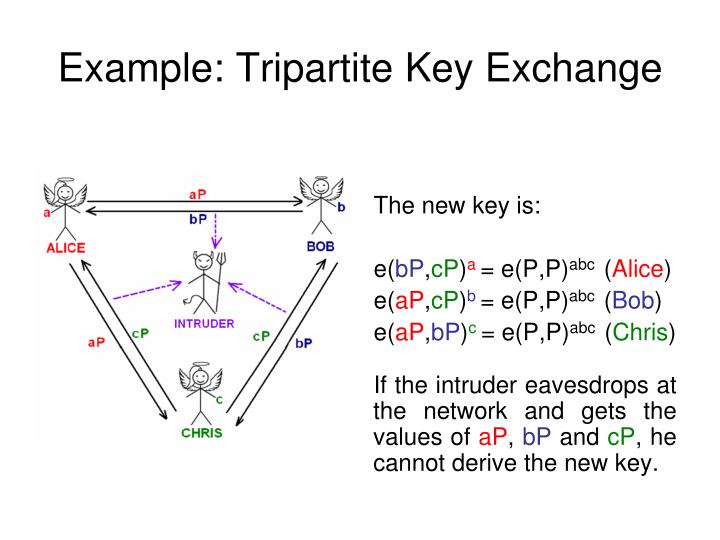
- CDH (Computation Diffie-Hellman) is still hard as we can’t find if we know , , .
- Bilinear Diffie-Hellman Problem: Given , compute
Prerequisites
- Fermat’s Little Theorem: for a prime p, and any positive integer a,
- Additive Group: set of numbers with operation defined on addition
- Multiplicative group: set of numbers with operation defined on multiplication
- Order of Multiplicative group
Resources
- Vitalik: Exploring Elliptic Curve Pairings
- Statebox’s Elliptic Curve Pairings
- https://crypto.stanford.edu/pbc/thesis.pdf
- https://people.csail.mit.edu/alinush/6.857-spring-2015/papers/bilinear-maps.pdf
- Fundamental Concepts Underlying Elliptic Curves (Level 2): Divisors and Pairings
- Why pairings are used?
- Basics of Pairings - Dan Boneh
- Pairings for beginners
- Intro to Pairings